Press release
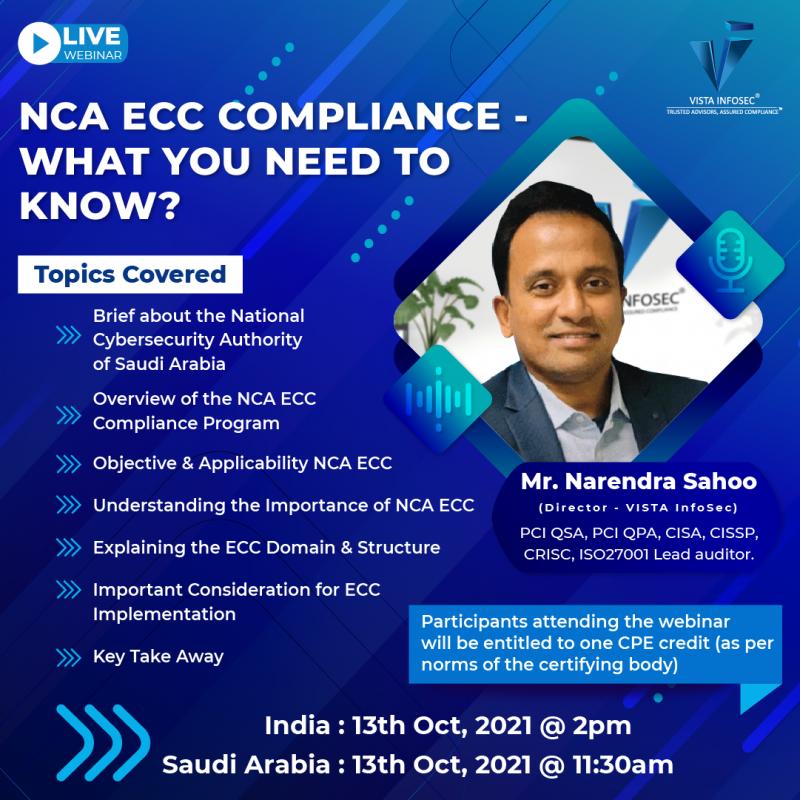
NCA ECC Compliance - What you Need to Know?
Saudi Arabia ranks among the top few countries in the world that are known to take its Cybersecurity programs very seriously. Committed to building a safe haven for businesses in the country, the National Cybersecurity Authority (NCA) of Saudi Arabia introduced the Essential Cybersecurity Controls Compliance Programs. Taking into account the best Cybersecurity practices globally, analyzing the major Cybersecurity incidents prevailing in the country, and also considering the opinions of various prominent businesses, the NCA developed a well-articulated and comprehensive ECC Compliance program. With the enforcement and mandate of complying with the standard, all the government organizations in the Kingdom of Saudi Arabia are required to strategically adhere to the outlined framework.Dissecting the framework and explaining the ECC framework in detail, VISTA InfoSec is conducting an informative webinar on “NCA ECC Compliance - What you Need to Know?” for the benefit of our viewers and businesses in Saudi Arabia. We will be conducting a live and interactive session, wherein any individuals can participate and learn about the standard and ways to achieve compliance. The forum will also be open for queries pertinent to NCA ECC, where individuals can clear their doubts about the regulation. Get some useful tips and techniques on ways of achieving compliance from our in-house expert - Mr. Narendra Sahoo (PCI QSA, PCI QPA, PCI SSFA, CISSP, CISA, CRISC), who is also the Founder and Director of VISTA InfoSec.
Explaining in detail, Mr. Sahoo will guide organizations in understanding the core requirements of the regulation and necessary steps to be taken for achieving and maintaining NCA ECC Compliance. Given below are some of the key highlights that we plan to cover in our multi-time zone webinar.
Topics Covered
Brief about the National Cybersecurity Authority of Saudi Arabia
Overview of the NCA ECC Compliance Program
Objective & Applicability NCA ECC
Understanding the Importance of NCA ECC
Explaining the ECC Domain & Structure
Important Consideration for ECC Implementation
Key Take Away
Highlights of our Webinar
Live Q&A session
Participants attending the webinar will be entitled to one CPE credit (as per norms of the certifying body)
Book your seat! Limited Seats Available! FREE Registration!
Registration Link
Date: 13th oct,2021
Time: Time : India 2pm & Saudi Arabia 11:30 AM
https://register.gotowebinar.com/register/4776989213568210957
VISTA InfoSec
Office 48 Al Mamzar Business Center
Al Mamzar Center, Dubai, UAE
Tel 04-2035048 Fax 04-2035060
We have been in the industry for almost two decades (since 2004) serving clients in securing their IT Infrastructure and assisting them in their Compliance obligations. Our service offerings include Information Security Consultation, Compliance and Advisory Services. Whether your business is local or global, we can help you meet Regulatory Standards for virtually any market around the globe. For our industry-winning Compliance process and customer-centric approach, we hold extensive global accreditations and recognitions for our services.
This release was published on openPR.
Permanent link to this press release:
Copy
Please set a link in the press area of your homepage to this press release on openPR. openPR disclaims liability for any content contained in this release.
You can edit or delete your press release NCA ECC Compliance - What you Need to Know? here
News-ID: 2412531 • Views: …
More Releases from VISTA InfoSec
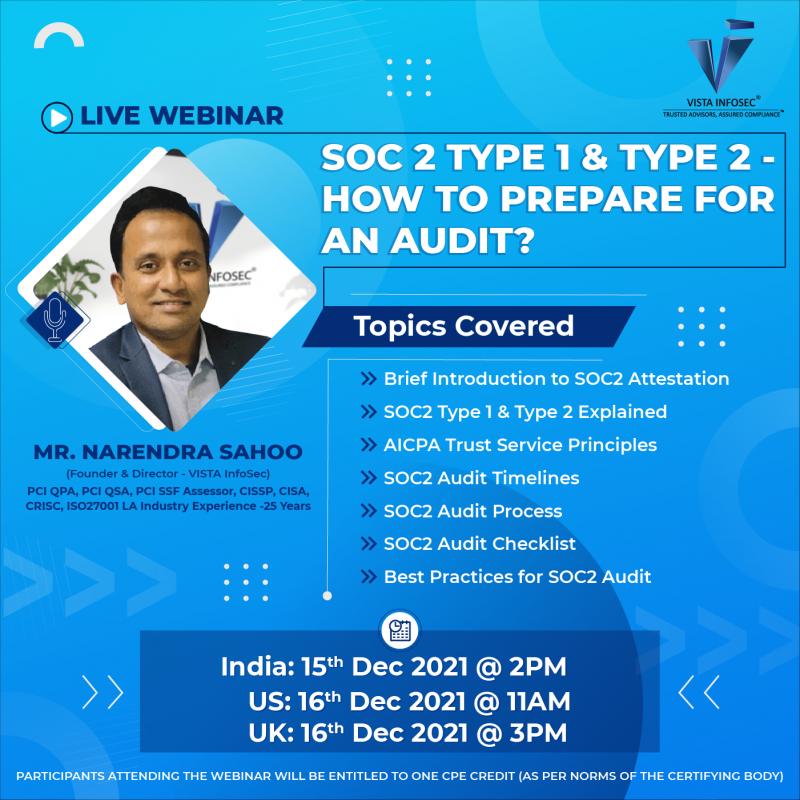
SOC 2 Type 1 & Type 2- How to Prepare for Audit?
Service Organizations must prioritize and consider investing in the technical process of SOC 2 Audit and Attestation. SOC2 Attestation obtained from an independent AICPA qualified CPA firm is one way to assure customers that their data is safe with the company. But, when it comes to achieving SOC2 Attestation, the entire audit process can be quite overwhelming for Service Organizations. Performing and preparing for the SOC2 Audit is crucial to…

Integrating ISO27701 in PIMS to Improve Data Privacy.
Organizations are today highly regulated by various international data privacy laws and regulations. They are expected to prioritize data security to uphold the privacy of consumer data. Keeping this in mind, organizations are increasingly implementing Privacy Information Management Systems (PIMS). Today, PIMSA is seen as an effective approach towards ensuring the privacy and security of personal data. It helps organizations manage personal data in line with various regulations, standards,…
More Releases for Cybersecurity
Fortem Cybersecurity, the New Global Cybersecurity Brand from Maguen Group, Offi …
Fortem Cybersecurity brings a new era of digital defense.
Image: https://www.globalnewslines.com/uploads/2025/11/c0679b6403ecd7de771af2a356c54f29.jpg
Maguen Group [https://www.maguengroup.com/?lang=en], a leading Mexican private security company with over 17 years of operational excellence and ethical leadership, is proud to announce the launch of its new global cybersecurity brand, Fortem Cybersecurity [https://fortem-security.com/]. This launch comes as part of Maguen Group's plans to expand its presence and democratize cybersecurity.
With the launch of Fortem Cybersecurity, Maguen Group continues its commitment to…
Rising Global Cybersecurity Threats Propel Growth In Military Cybersecurity Mark …
The Military Cybersecurity Market Report by The Business Research Company delivers a detailed market assessment, covering size projections from 2025 to 2034. This report explores crucial market trends, major drivers and market segmentation by [key segment categories].
What Is the Military Cybersecurity Market Size and Projected Growth Rate?
The size of the military cybersecurity market has seen significant growth recently. The market is predicted to increase from a worth of $14.05 billion…
Rising Global Cybersecurity Threats Propel Growth In Military Cybersecurity Mark …
What market dynamics are playing a key role in accelerating the growth of the military cybersecurity market?
The surge in cyberattacks is projected to drive the expansion of the military cybersecurity market. A cyberattack, an illicit attempt to infiltrate a computer system or network to cause disruption, can result in data theft, deliberate machine impairment, or use a breached system to launch further attacks. The military's smooth operation hinges on the…
Top Cybersecurity Expert Nandy Bo Publishes Groundbreaking Freelancing Guide for …
NYC, New York, USA - Renowned cybersecurity consultant and top-rated Upwork freelancer, Nandy Bo, has launched his highly anticipated book, Master Upwork: Achieve Financial Freedom Through a Freelance Cybersecurity Career . This comprehensive guide provides aspiring and seasoned freelancers with the tools and strategies needed to thrive in today's competitive freelance economy, particularly in high-demand fields like cybersecurity and compliance.
With over 16 years of experience, Nandy Bo has established himself…
Cybersecurity Mesh Market Report 2024 - Cybersecurity Mesh Market Demand, Trends …
"The Business Research Company recently released a comprehensive report on the Global Cybersecurity Mesh Market Size and Trends Analysis with Forecast 2024-2033. This latest market research report offers a wealth of valuable insights and data, including global market size, regional shares, and competitor market share. Additionally, it covers current trends, future opportunities, and essential data for success in the industry.
According to The Business Research Company's, The cybersecurity mesh market size…
Cybersecurity Experts Provide Insight on the ROI of Managed Cybersecurity Servic …
Image: https://www.getnews.info/wp-content/uploads/2024/09/1727067882.jpeg
Cybersecurity professionals detail how managed cybersecurity services can provide significant returns on investment (ROI) by offering cost-effective, risk-reducing solutions that enhance an organization's security posture.
Columbia, MD - September 23, 2024 - Shield 7, a leader in cybersecurity services [https://shield7.com/], has recently released a blog titled "The ROI of Managed Cybersecurity Services: A Comparative Analysis." This comprehensive analysis explores how managed cybersecurity services can offer significant returns on investment (ROI)…